AXA: €2.3M from CNIL. Lloyd’s: repeated enforcement actions. Generali: regulatory orders across three jurisdictions. Insurance is no longer exempt from banking-grade AML scrutiny — and transaction monitoring systems calibrated on simple domestic profiles are producing either a flood of false positives or dangerous blind spots.
Your Transaction Monitoring Was Built for Banking — Not Insurance
I have spent enough time inside insurance compliance operations to recognize the pattern. A life insurance policy pays out €4.2M to a beneficiary in Luxembourg. The beneficiary is a trust registered in Liechtenstein. The original policyholder listed a tax domicile in Switzerland but made premium payments from a UAE bank account. The transaction monitoring system flags every single movement in the chain — not because any of them are suspicious, but because the system has never seen a legitimate multi-jurisdictional insurance transaction before.
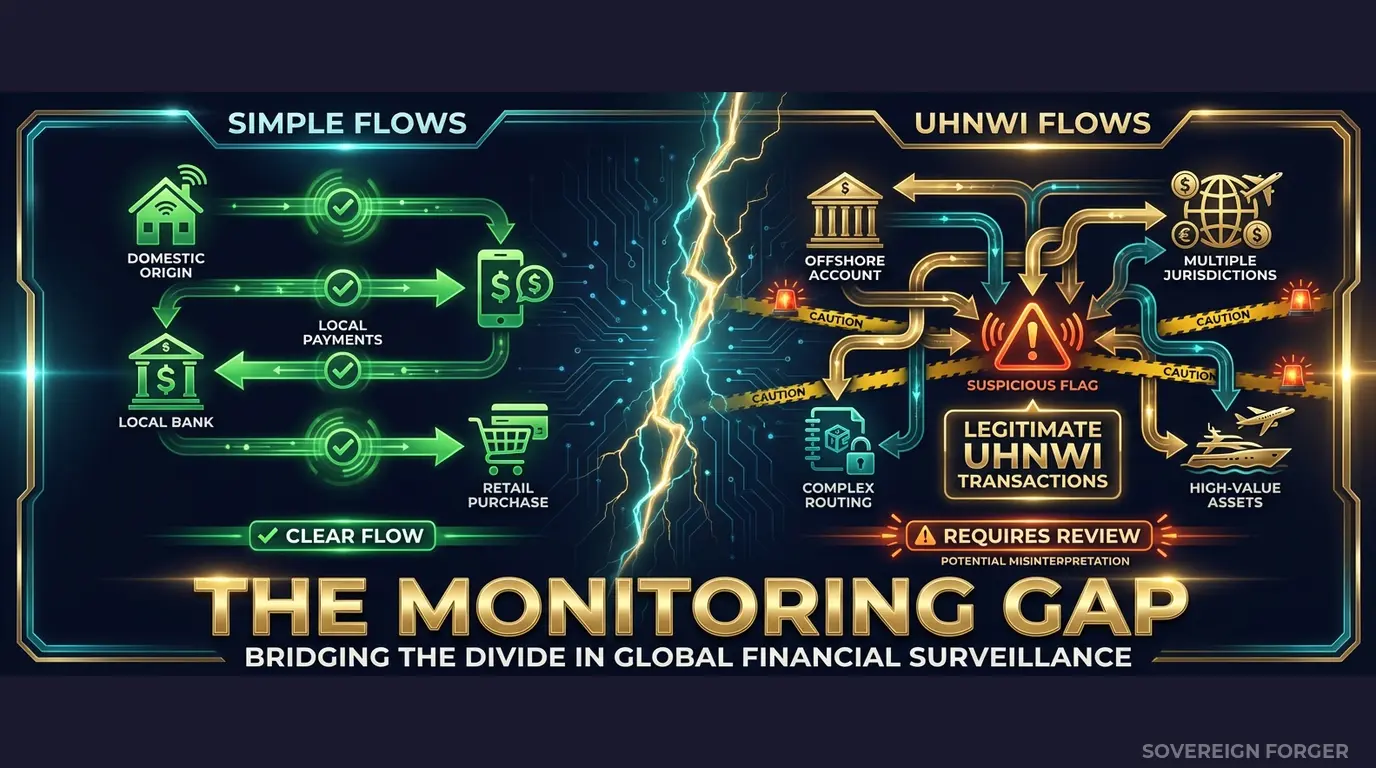
This is the core problem. Insurance companies adopted transaction monitoring systems designed for retail banking. Those systems were trained on data where a normal transaction is a domestic salary deposit and an abnormal transaction is a large cross-border wire. In insurance, the baseline is fundamentally different. A single high-value life policy can involve premium payments from one jurisdiction, policy ownership in a second, beneficiary structures in a third, and payout destinations in a fourth. That is not money laundering — that is how wealthy policyholders actually structure their affairs.
But the monitoring system does not know this, because it was never shown what legitimate multi-jurisdictional insurance wealth flows look like.
The result is two-fold. First, compliance teams drown in false positives. I have seen teams where 94% of flagged transactions are dismissed after manual review — not because the team is cutting corners, but because the monitoring thresholds were calibrated against structurally simple test data that never included offshore vehicles, trust-owned policies, or cross-border premium financing. Every legitimate complex transaction triggers an alert. The team reviews. The team clears. Repeat, eight hundred times a month.
Second — and this is the part that keeps compliance officers awake — the real suspicious transactions hide inside the noise. When your analysts spend their days clearing false positives on legitimate UHNWI policy transactions, they develop alert fatigue. The genuinely suspicious pattern — a series of single-premium life policies used to convert large cash sums into clean insurance payouts — gets the same two-minute review as every other flag. It looks like just another cross-border policy transaction, because every cross-border policy transaction looks suspicious to a system that was never trained on legitimate ones.
EIOPA and national regulators understand this. The European Insurance and Occupational Pensions Authority has been systematically extending banking-grade AML requirements to insurance. The 5th Anti-Money Laundering Directive explicitly brought life insurance under the same Customer Due Diligence requirements as banks. National regulators — BaFin, ACPR, the FCA — are conducting thematic reviews of insurance AML controls. They are not asking whether you have a transaction monitoring system. They are asking whether your system can distinguish between a legitimate UHNWI policy structure and a laundering vehicle. If your system was calibrated on flat domestic data, the honest answer is: it cannot.
The insurance-specific laundering vectors are well-documented. Single-premium life policies as value stores. Premium financing through offshore entities. Early surrender of policies for “clean” payouts. Policy loans against inflated valuations. Free-look period abuse — purchasing and cancelling policies to generate refund checks from a regulated institution. These are not edge cases. They are the specific patterns that EIOPA has identified as high-risk. If your transaction monitoring data does not contain profiles that would naturally generate these transaction patterns, your system has never been tested against the threats regulators are specifically looking for.
Three Approaches That Leave Insurance Compliance Exposed
Insurance companies face a unique challenge: the industry arrived late to AML compliance, and the solutions available were built for a different sector. I have evaluated the test data strategies of insurers across Europe and Asia-Pacific, and the same three failing patterns appear everywhere.
Using copies of policyholder data. Some compliance teams extract real policyholder records into test environments for monitoring calibration. In banking, this was already a GDPR Article 25 violation. In insurance, it is worse — policyholder data includes health information, beneficiary relationships, and payout histories that are classified as special category data under GDPR Article 9. Moving this data into a test environment with broader access controls does not just violate privacy regulations — it creates a liability that no Data Protection Officer should accept. And under the EU AI Act, effective August 2026, using this data to train monitoring models requires documented provenance and governance that most insurers cannot provide.
Using anonymized policyholder data. The UHNWI policyholder population is small and structurally distinctive. There are approximately 265,000 UHNWIs globally, and the subset holding high-value life insurance policies is smaller still. When a test record shows a net worth above $50M, a Cayman Islands trust as policy owner, premium payments from Singapore, and a tax domicile in Switzerland — stripping the name does not anonymize the profile. The combination of jurisdiction, wealth tier, offshore structure, and policy characteristics can uniquely identify the policyholder. A regulator or a motivated adversary with access to public wealth registries can re-identify these records with alarming accuracy.
Using generic synthetic generators. Platform-based synthetic data tools generate profiles that reflect retail insurance customers — single jurisdiction, single beneficiary, domestic premium payments. They produce a bell curve of wealth distribution when real UHNWI wealth follows a Pareto distribution. They generate offshore exposure at 0% when real UHNWI policyholders in certain niches have offshore structures in 60-80% of cases. Your transaction monitoring system trains on these flat profiles and learns that any cross-border premium payment is anomalous. Then a real UHNWI client arrives with premium payments routed through three jurisdictions — a perfectly normal structure for their wealth archetype — and the system flags it as high risk. Multiply this by every complex policyholder in your book, and you understand why the false positive rate is 94%.
Real Data vs. Anonymized vs. Born-Synthetic
| Dimension | Real Policyholder Data | Anonymized | Born-Synthetic |
|---|---|---|---|
| PII present | Yes (incl. health data) | Residual | None |
| Re-identification risk | Certain | Probable (UHNWI) | Impossible |
| GDPR Art. 25 compliant | No | Disputed | Yes |
| GDPR Art. 9 (special category) | Violation | Violation | Not applicable |
| EU AI Act Art. 10 | Violation | Unclear | Compliant |
| Certifiable for auditors | No | No | Yes (Certificate of Origin) |
| Offshore structure realism | High (real data) | Degraded by stripping | High (archetype-driven) |
| Fine exposure | Up to 4% global revenue | Up to 4% global revenue | Zero |
Born-Synthetic KYC Data Built for Insurance Transaction Monitoring Calibration
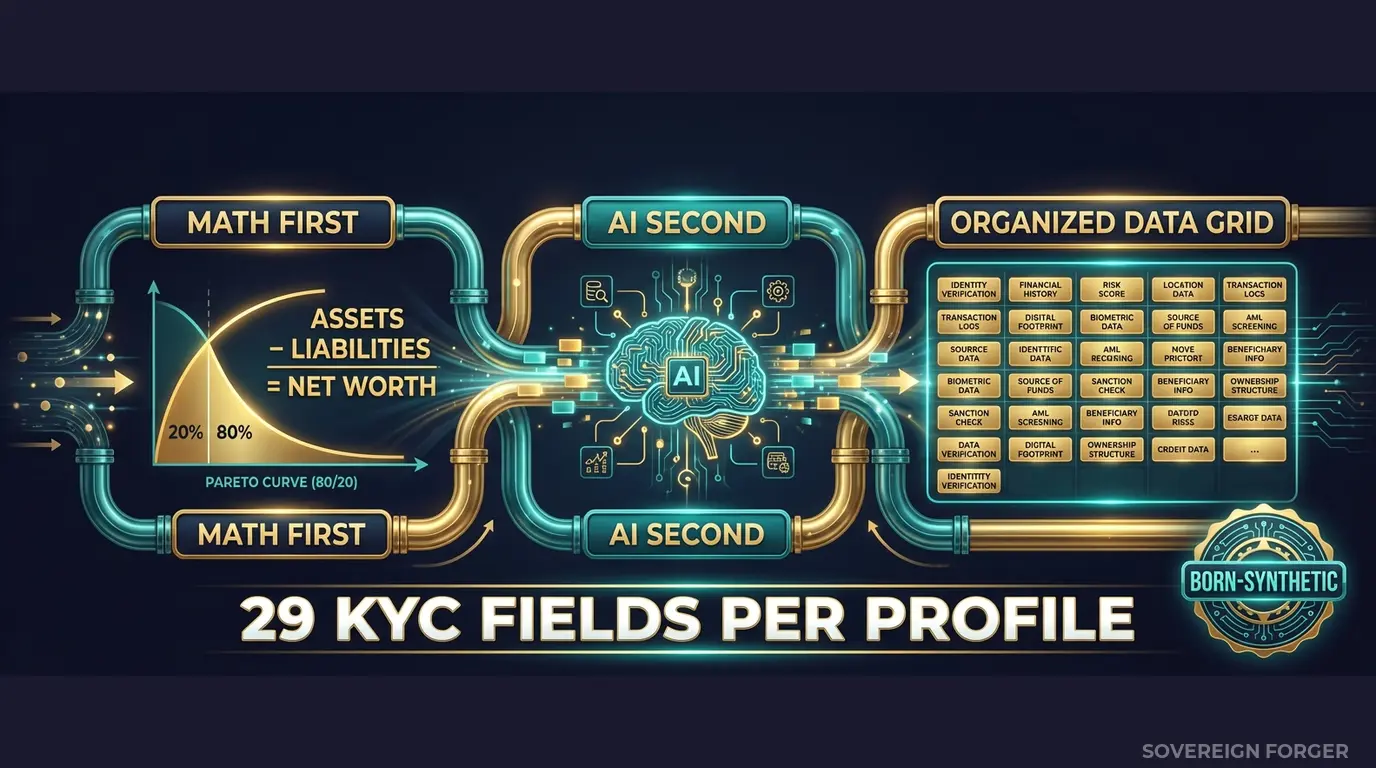
The core problem with insurance transaction monitoring is calibration. Your system needs to learn the difference between a suspicious transaction and a legitimate complex one. That distinction depends entirely on the profile behind the transaction — and if the profiles in your test data do not reflect the structural complexity of real UHNWI policyholders, the system cannot learn the distinction.
I built the Sovereign Forger pipeline to solve exactly this problem. Every profile is generated from mathematical constraints — not derived from any real person, not anonymized from any real policyholder. The generation pipeline works in two stages:
Math First. Net worth follows a Pareto distribution — the actual shape of wealth concentration, not a bell curve. Asset allocations are computed within algebraic constraints: Assets – Liabilities = Net Worth, by construction. Property values, equity holdings, cash liquidity, and offshore vehicle valuations are distributed according to the wealth archetype and geographic niche. Every balance sheet balances on every record. This means your transaction monitoring system can use the wealth composition to determine whether a given transaction is proportionate to the profile — because the profile’s financial structure is internally consistent.
AI Second. A local AI model running entirely offline adds narrative context — biography, profession, philanthropic focus — after the financial figures are locked. The AI never touches the numbers. It enriches the profile with culturally coherent details that match the geographic niche, wealth tier, and archetype. A Swiss private banker and a Middle Eastern sovereign family member have different wealth structures, different offshore preferences, and different transaction patterns — and the profiles reflect this.
How This Solves Transaction Monitoring for Insurance
Threshold calibration. When your monitoring system is trained on profiles that include realistic multi-jurisdictional exposure — offshore vehicles in BVI, tax domicile in a different country, asset composition split across property, equity, and cash in multiple currencies — it learns that cross-border flows are normal for certain client types. The system can then set thresholds that flag genuinely unusual activity rather than flagging every complex but legitimate structure.
False positive reduction. The 29 KYC fields per profile include `offshore_jurisdiction`, `offshore_vehicle`, `tax_domicile`, `assets_composition`, and `high_risk_jurisdiction_flag`. Your monitoring system can use these fields to contextualize transactions. A premium payment from Dubai to a policy held in Luxembourg is suspicious if the policyholder is a domestic retail customer. It is entirely normal if the policyholder has tax domicile in the UAE, assets distributed across Middle East and European jurisdictions, and a wealth archetype consistent with sovereign family structures. The difference between a false positive and a real alert is in the profile — and Born-Synthetic profiles provide the structural depth your system needs to make that distinction.
Edge case coverage. The dataset includes 31 wealth archetypes across 6 geographic niches. This means your monitoring system encounters profiles that generate the exact patterns regulators are concerned about: PEP-adjacent connections, high-risk jurisdiction exposure, multi-layered offshore structures, and wealth compositions that would naturally produce the premium payment patterns, surrender patterns, and beneficiary structures that characterize insurance-specific money laundering. Your system learns to distinguish these patterns from legitimate UHNWI activity — because it has seen both.
Audit-ready documentation. When EIOPA or your national regulator asks how your transaction monitoring system was calibrated, you need to demonstrate that the test data was representative of your actual risk exposure. Born-Synthetic data ships with a Certificate of Sovereign Origin documenting the generation methodology, zero PII lineage, and regulatory alignment. The certificate proves that your system was trained on structurally complex data — not flat domestic profiles that would never trigger the scenarios regulators care about.
29 Fields Designed for Transaction Monitoring Calibration
Every KYC-Enhanced profile includes the fields your monitoring system needs to contextualize alerts:
Identity & Geography: full_name, residence_city, residence_zone, tax_domicile
Wealth Structure: net_worth_usd, total_assets, total_liabilities, property_value, core_equity, cash_liquidity, assets_composition, liabilities_composition
Professional Context: profession, education, narrative_bio, philanthropic_focus
Offshore Exposure: offshore_jurisdiction, offshore_vehicle
KYC Signals: kyc_risk_rating, pep_status, pep_position, pep_jurisdiction, sanctions_screening_result, sanctions_match_confidence, adverse_media_flag, source_of_wealth_verified, sow_verification_method, high_risk_jurisdiction_flag
Every KYC field is deterministically derived from the profile’s archetype, niche, net worth, and jurisdiction. A commodity trader in the Middle East niche with net worth above $200M gets different risk signals, different offshore exposure, and different PEP probability than a tech founder in Silicon Valley. This is not random noise — it is structural coherence that mirrors how real wealth determines real risk profiles.
Built for Insurance Transaction Monitoring at Scale
6 Geographic Niches: Silicon Valley, Old Money Europe, Middle East, LatAm, Pacific Rim, Swiss-Singapore — each with culturally coherent wealth patterns that produce different transaction monitoring profiles. A Middle Eastern sovereign family and a Swiss multi-family office generate fundamentally different premium payment patterns, beneficiary structures, and cross-border flows.
31 Wealth Archetypes: Tech founders, private bankers, commodity traders, family office managers, real estate developers, sovereign family members — the actual client profiles that generate complex insurance transactions. Each archetype has a distinct wealth composition, offshore preference, and risk signal distribution.
KYC Signal Distribution: Risk ratings, PEP statuses, sanctions screening results, and source-of-wealth verification methods distributed with realistic frequencies by niche. The Middle East niche has ~29% PEP exposure. LatAm has ~84% high-risk rating. Europe and Swiss-Singapore have ~48% low-risk. These distributions match real-world patterns — your monitoring system calibrates against realistic signal proportions, not uniform randomness.
Multi-Jurisdictional Depth: Every profile with offshore exposure includes specific jurisdiction, vehicle type, and tax domicile — the exact fields your monitoring system needs to determine whether a cross-border premium payment is consistent with the policyholder’s wealth structure or genuinely anomalous.
Pricing
| Tier | Records | Price | Best For |
|---|---|---|---|
| Compliance Starter | 1,000 | $999 | Monitoring threshold POC |
| Compliance Pro | 10,000 | $4,999 | Full calibration suite |
| Compliance Enterprise | 100,000 | $24,999 | AI model training + production calibration |
No SDK. No API key. No sales call. Download a file, load it into your monitoring platform, and start calibrating thresholds against structurally realistic profiles.
Why This Matters Now for Insurance
The regulatory perimeter is expanding. EIOPA’s thematic reviews are systematically extending banking-grade AML expectations to insurance. The 5th Anti-Money Laundering Directive brought life insurance under full CDD requirements. The 6th AMLD expanded predicate offences. National regulators — BaFin in Germany, ACPR in France, the FCA in the UK — are conducting targeted inspections of insurance AML controls. The question is no longer whether your insurer needs transaction monitoring — it is whether your monitoring can withstand regulatory scrutiny.
The fines are arriving. AXA received a €2.3M fine from CNIL — and that was a data protection action, not even an AML enforcement. Lloyd’s has faced repeated regulatory interventions. The FCA’s Dear CEO letters to insurance firms have become increasingly specific about transaction monitoring expectations. BaFin has ordered German insurers to remediate AML controls with explicit deadlines. The enforcement trajectory is clear: what happened to neobanks in 2023-2024 is happening to insurance in 2025-2026.
The EU AI Act adds a second layer. Effective August 2026, financial AI is classified as high-risk under Annex III. If your transaction monitoring uses machine learning — and increasingly, it does — Article 10 requires documented governance of training data. Provenance, bias assessment, GDPR compliance. If your monitoring model was trained on real or anonymized policyholder data, you need to prove compliance on both GDPR and the AI Act simultaneously. Born-Synthetic data eliminates this entire category of risk: zero PII means zero GDPR exposure, and documented generation methodology satisfies Article 10 provenance requirements.
The balance sheet test is open source. Every Sovereign Forger record passes algebraic validation: Assets – Liabilities = Net Worth. Run the Balance Sheet Test on our data, then run it on your current test data. If your current data does not pass this test, your monitoring system is calibrating against financially inconsistent profiles — profiles where the numbers do not add up, which means the transaction proportionality checks built on those numbers are meaningless.
Every dataset ships with a Certificate of Sovereign Origin — documenting the born-synthetic methodology, zero PII lineage, and regulatory alignment. When your regulator or auditor asks “how did you calibrate your transaction monitoring?”, you hand them the certificate. It documents that your system was trained on structurally complex, born-synthetic profiles with zero lineage to real policyholders.
Calibrate Your Transaction Monitoring
Download 100 free KYC-Enhanced UHNWI profiles with realistic multi-jurisdictional exposure, offshore structures, and wealth composition. Use them to baseline your monitoring thresholds.
Feed them into your transaction monitoring system. Count how many trigger false positives that your analysts would dismiss in under two minutes. Count how many contain structural complexity — PEP connections, high-risk jurisdictions, multi-layered offshore vehicles — that your current test data has never included.
The first number tells you how much analyst time you are wasting. The second tells you how large your monitoring blind spot actually is.
No credit card. No sales call. Just your work email.
Related reading: DORA Synthetic Data Requirements for Resilience Testing — how DORA Article 24-25 mandates synthetic data for threat-led penetration testing.
Frequently Asked Questions
What makes insurance transaction monitoring testing different from banking transaction monitoring?
Insurance transactions include premium payments, claims disbursements, policy surrenders, annuity distributions, and reinsurance flows — patterns fundamentally different from banking wire transfers. Testing with banking-derived synthetic data misses insurance-specific risk indicators like premium structuring (splitting large payments to avoid reporting thresholds), claims fraud patterns, and suspicious early surrender of investment-linked policies. Sovereign Forger profiles provide the UHNWI financial complexity that generates realistic insurance transaction edge cases.
How does born-synthetic data help insurers reduce false positive rates in transaction monitoring?
False positives in insurance transaction monitoring often stem from legitimate UHNWI behavior being flagged as suspicious — large premium payments, cross-border policy structures, and trust-based ownership arrangements. Born-synthetic profiles include realistic asset compositions, offshore structures, and source of wealth data that mirror these legitimate patterns. By calibrating alert thresholds against statistically representative synthetic data, compliance teams can reduce false positive rates without weakening detection of genuinely suspicious activity.
Does DORA require insurers to test transaction monitoring systems with synthetic data?
DORA Articles 24-25, enforceable since January 2025, require financial entities including insurers to conduct regular ICT resilience testing of critical systems. Transaction monitoring is a critical AML system under both DORA and the EU Anti-Money Laundering Authority (AMLA) framework. While DORA does not mandate synthetic data specifically, it explicitly anticipates its use for threat-led penetration testing — and using production data in test environments creates the GDPR compliance contradiction that synthetic data resolves.
What volume of synthetic transaction data is needed to validate insurance monitoring alert rules?
Alert rule validation requires sufficient volume to generate statistically meaningful distributions of both normal and suspicious patterns. Using Sovereign Forger’s 100,000 UHNWI profiles per niche as the base, insurance teams can derive transaction histories that produce the full range of alert scenarios — from high-frequency premium structuring to cross-border claims disbursement anomalies. The Compliance Enterprise tier ($24,999 per niche) provides the depth needed for comprehensive rule validation across all alert categories.
Can synthetic transaction monitoring data be used for both regulatory reporting testing and system UAT?
Yes. Sovereign Forger’s born-synthetic approach generates profiles with internally consistent financial data — assets minus liabilities equals net worth by algebraic construction. This mathematical integrity means the same dataset works for both user acceptance testing (validating system behavior) and regulatory reporting testing (verifying STR/SAR generation logic). A single dataset investment serves dual purposes without the data governance overhead of maintaining separate anonymized test environments.
Learn more about insurance transaction monitoring synthetic data and how Born Synthetic data addresses this in our glossary and comparison guides.