Block: $120M. Western Union: $586M. MoneyGram: $125M. PayPal: repeated enforcement actions. Every one of these penalties traces back to the same root cause — sanctions screening systems that were never tested against the name complexity, jurisdictional layering, and PEP-adjacent connections that trigger real-world failures.
Your Sanctions Screening Engine Has Never Been Properly Tested
I have sat in a room where a payment processor’s compliance team demonstrated their sanctions screening system to a regulator. The system looked impressive: sub-second response times, fuzzy matching algorithms, real-time OFAC and EU sanctions list integration, configurable risk thresholds. Every test transaction cleared or flagged correctly. The demo was flawless.
Six weeks later, a $2.3M wire transfer cleared through the same system from a shell company in the British Virgin Islands controlled by a PEP-adjacent individual whose transliterated name matched a consolidated sanctions list entry at 87% confidence — just below the threshold the team had calibrated using their test data. The system let it through. The regulator did not.
This is the pattern I see repeatedly across payment processors. The sanctions screening engine itself is often sophisticated. The problem is what it was tested against. When your test profiles contain names like “John Smith” and “Maria Garcia,” single-jurisdiction exposure, zero offshore vehicles, and no PEP connections, you are calibrating your fuzzy matching thresholds, your risk scoring weights, and your alert escalation rules against a population that bears no resemblance to the transactions that actually trigger sanctions violations.
Payment processors face a unique version of this problem. Unlike banks that onboard clients and monitor them over time, payment processors see transactions at massive scale with minimal client context. A single processor might handle millions of cross-border transactions per day across dozens of jurisdictions. Every transaction is a potential sanctions screening event. Every screening event depends on the quality of the matching algorithm. And the quality of the matching algorithm depends entirely on the data it was tested and calibrated against.
The numbers tell the story. Western Union paid $586M in penalties — not because their screening technology was primitive, but because their systems failed to catch transactions involving sanctioned jurisdictions and PEP-connected individuals whose profiles were structurally more complex than anything in their test environment. Block paid $120M to FinCEN and multiple state regulators for similar failures in their Cash App business. MoneyGram’s $125M settlement with the DOJ and FTC centered on the same gap: adequate screening technology, inadequate testing against realistic threat profiles.
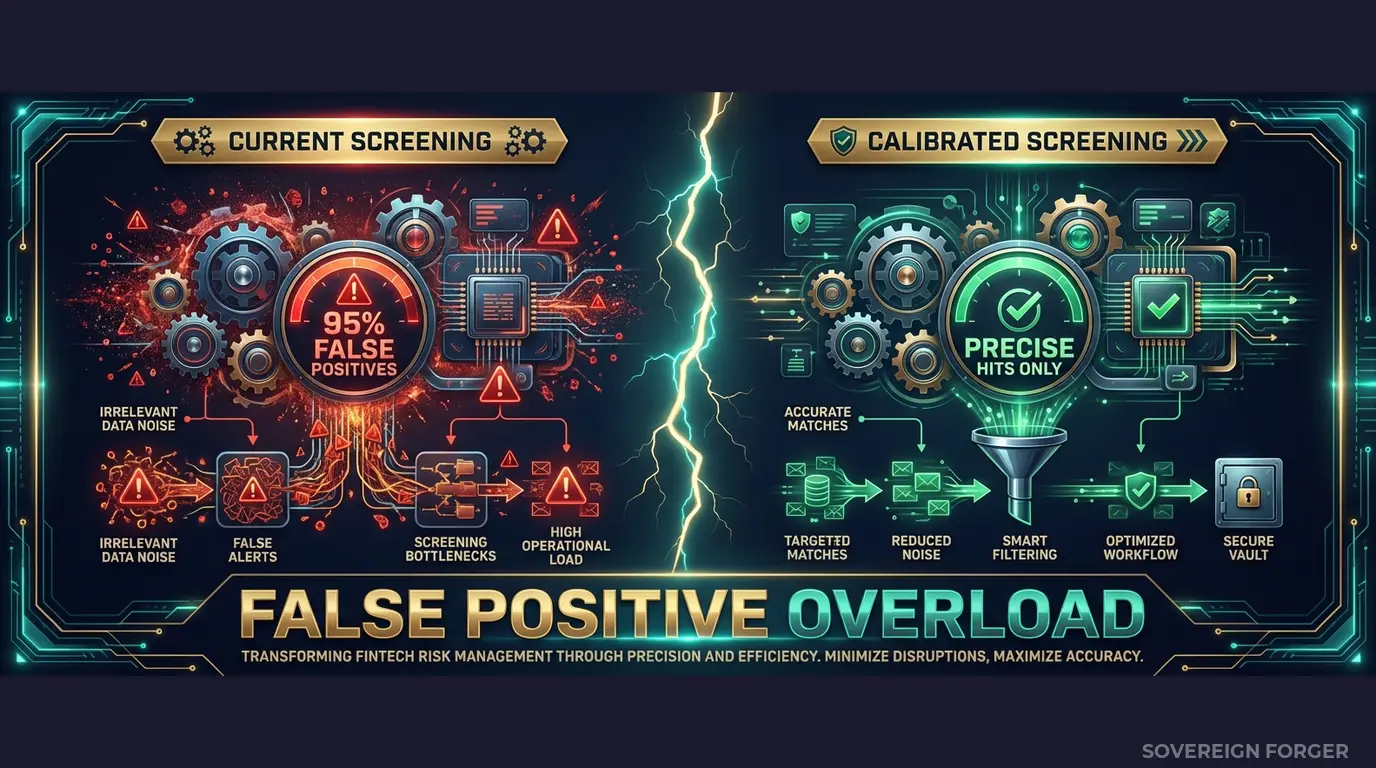
The false positive problem is the mirror image of the same failure. When your screening system has never been calibrated against genuinely complex but legitimate profiles — a tech founder with dual nationality, offshore holdings in Singapore and the Cayman Islands, and a family member who held a minor government position — it cannot distinguish between suspicious and merely complex. The result is either a flood of false positives that overwhelms your compliance team, or loosened thresholds that let genuinely suspicious transactions through. Both outcomes lead to the same place: regulatory action.
Three Approaches That Leave You Exposed
I have audited the sanctions screening test environments at payment processors ranging from Series B fintechs to publicly traded companies processing billions per quarter. The test data falls into the same three categories every time — and every category has the same fundamental flaw.
Using copies of production transaction data. Some teams extract real transaction records and client profiles into their screening test environment. This creates an immediate GDPR Article 25 violation — personal data in environments with weaker access controls, broader team access, and often insufficient logging. For payment processors operating across the EU, the August 2026 EU AI Act enforcement adds a second layer of exposure: if your screening AI models train on this data, Article 10 requires documented governance of training data provenance. You cannot document the provenance of data you were not supposed to have in a test environment.
Using anonymized transaction and client data. Stripping names and account numbers from real high-value client profiles does not eliminate re-identification risk. With only 265,000 UHNWIs globally, the combination of transaction volume, jurisdiction pairs, currency patterns, and business type can uniquely identify individuals even without direct identifiers. For sanctions screening specifically, this creates a paradox: the fields you need for meaningful screening tests — name variants, jurisdictions, entity types — are precisely the fields that make re-identification trivial. A regulator can argue, correctly, that your “anonymized” screening test data is merely pseudonymized, and GDPR applies in full.
Using generic synthetic generators. Platform-based generators produce structurally flat profiles — single-jurisdiction exposure, anglicized names, no offshore vehicles, no entity layering. They generate retail payment users with bigger numbers, not actual UHNWI wealth architecture with the multi-jurisdictional complexity that breaks sanctions screening in production. Your fuzzy matching algorithm trains on “John Smith” and never encounters “Abdulrahman bin Khalid Al-Rasheed” with three transliteration variants, a family trust in Liechtenstein, and a cousin who served as deputy minister. When it does encounter that profile in production, it has no calibrated response.
Real Data vs. Anonymized vs. Born-Synthetic
| Dimension | Real Data | Anonymized | Born-Synthetic |
|---|---|---|---|
| PII present | Yes | Residual | None |
| Re-identification risk | Certain | Probable (UHNWI) | Impossible |
| GDPR Art. 25 compliant | No | Disputed | Yes |
| EU AI Act Art. 10 | Violation | Unclear | Compliant |
| Name complexity for screening | Real but illegal to use | Stripped or distorted | Culturally authentic, zero lineage |
| Multi-jurisdictional exposure | Yes but PII-bound | Partially retained | Full structural complexity |
| Certifiable for auditors | No | No | Yes (Certificate of Origin) |
| Fine exposure | Up to 4% global revenue | Up to 4% global revenue | Zero |
Born-Synthetic Sanctions Screening Data Built for Payment Processors
Every profile in the Sovereign Forger KYC dataset is generated from mathematical constraints — not derived from any real person. No real client was sampled, no real transaction was anonymized, no real name was modified. The profiles are born synthetic: compliant by construction, not by anonymization.
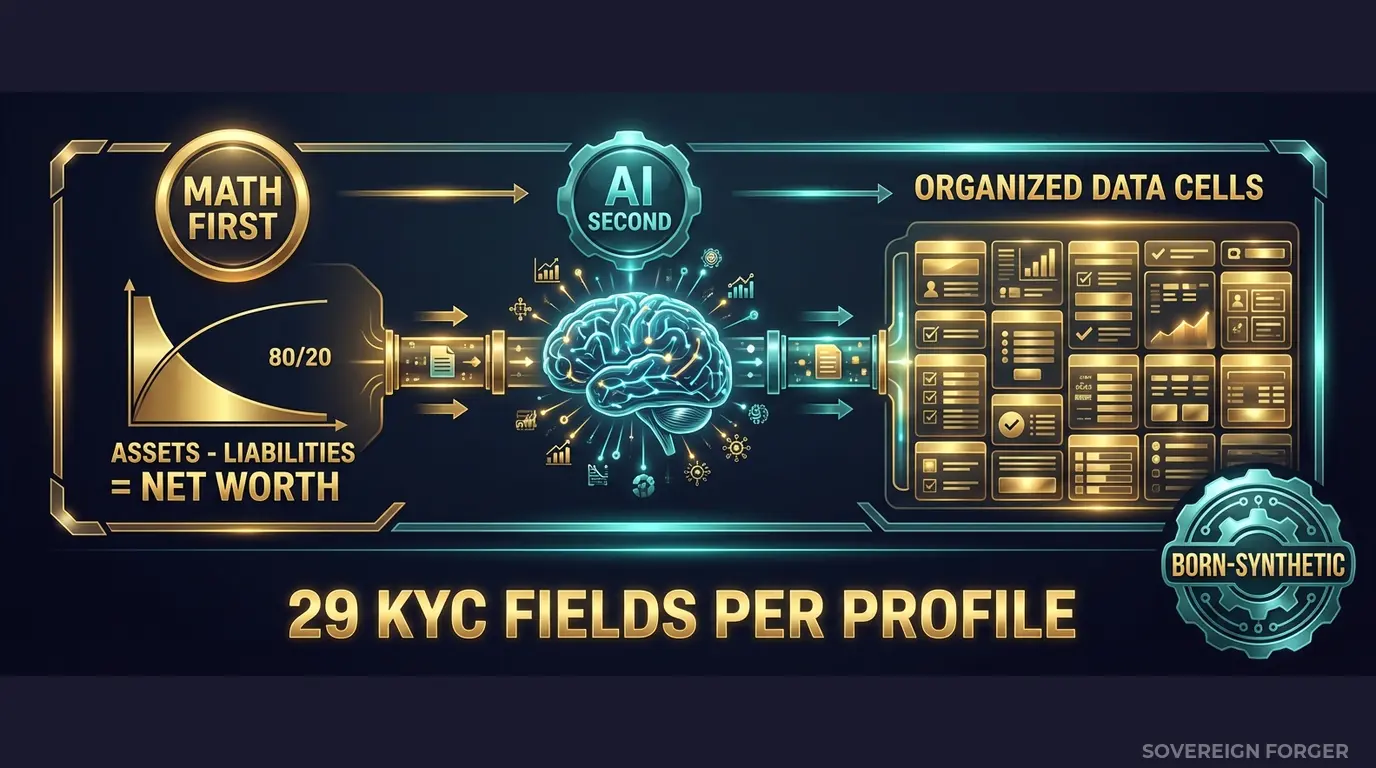
The generation pipeline works in two stages:
Math First. Net worth follows a Pareto distribution — the way real wealth is actually distributed, not a bell curve that clusters everyone around the median. Asset allocations are computed within algebraic constraints: Assets – Liabilities = Net Worth, by construction. Every balance sheet balances on every record. Zero exceptions. This matters for sanctions screening because the financial structure of each profile determines its jurisdictional exposure, offshore vehicle type, and risk signals. A profile with $800M in assets distributed across property, core equity, and offshore holdings behaves fundamentally differently in a screening engine than a profile with $2M in a single bank account.
AI Second. A local AI model running offline — no data ever touches the network — adds narrative context after the financial figures are locked. Biography, profession, philanthropic focus, education. The AI never touches the numbers. It enriches the profile with culturally coherent details that match the geographic niche and wealth tier, including name structures that reflect real onomastic patterns: patronymics, compound surnames, transliteration variants, honorifics.
Why This Matters for Sanctions Screening Specifically
Sanctions screening is a name-matching problem layered on top of a jurisdictional risk problem. Your screening engine needs to handle:
Name complexity. Arabic patronymics with multiple transliterations. Chinese names that may appear surname-first or given-name-first depending on the document source. Compound European surnames with particles (von, de, van) that may or may not be included. Hyphenated names where the order varies by jurisdiction. Sovereign Forger profiles use culturally authentic naming conventions across six geographic niches — not anglicized placeholders.
Jurisdictional layering. A single UHNWI profile may involve a residence city in London, a tax domicile in Switzerland, an offshore vehicle in the Cayman Islands, and a PEP jurisdiction in Saudi Arabia. Your screening engine must evaluate each jurisdiction against OFAC, EU, and UN sanctions lists simultaneously. If your test data contains profiles with a single jurisdiction, your engine has never been tested against this layering.
PEP-adjacent connections. PEP status is not binary. Sovereign Forger profiles include four PEP states — none, domestic, foreign, and international organization — with corresponding position and jurisdiction fields. A profile flagged as a domestic PEP with a position in a country that recently changed its sanctions status creates a screening edge case that generic test data never generates.
Sanctions signal calibration. Every Sovereign Forger KYC profile includes a `sanctions_screening_result` field (clear, potential_match, or confirmed_match) and a `sanctions_match_confidence` score (0-100). These values are deterministically derived from the profile’s archetype, niche, net worth, and jurisdiction — not randomly assigned. This means you can calibrate your screening thresholds against a population where the distribution of sanctions signals reflects realistic patterns by geography and wealth tier.
29 Fields Designed for Sanctions Screening Systems
Every KYC-Enhanced profile includes the fields your screening pipeline actually needs to evaluate:
Identity & Geography: full_name, residence_city, residence_zone, tax_domicile
Wealth Structure: net_worth_usd, total_assets, total_liabilities, property_value, core_equity, cash_liquidity, assets_composition, liabilities_composition
Professional Context: profession, education, narrative_bio, philanthropic_focus
Offshore Exposure: offshore_jurisdiction, offshore_vehicle
KYC & Sanctions Signals: kyc_risk_rating, pep_status, pep_position, pep_jurisdiction, sanctions_screening_result, sanctions_match_confidence, adverse_media_flag, source_of_wealth_verified, sow_verification_method, high_risk_jurisdiction_flag
Every KYC field is deterministically derived from the profile’s archetype, niche, net worth, and jurisdiction. A commodity trader in the Middle East with $500M net worth and an offshore vehicle in BVI generates different sanctions signals than a tech founder in Silicon Valley with $50M and a Delaware LLC — because the underlying risk profiles are structurally different.
Built for Payment Processor Sanctions Screening at Scale
6 Geographic Niches: Silicon Valley, Old Money Europe, Middle East, LatAm, Pacific Rim, Swiss-Singapore — each with culturally authentic naming conventions, jurisdiction-specific offshore structures, and wealth patterns that reflect real UHNWI populations. Your screening engine gets tested against transliterated Arabic names, compound European surnames, and Sino-Malay naming conventions — not 100,000 variations of “Jane Doe.”
31 Wealth Archetypes: Tech founders, sovereign family members, commodity traders, private bankers, real estate developers, shipping magnates — the actual client profiles that create sanctions screening edge cases in production. Each archetype has distinct jurisdictional exposure patterns, PEP likelihood, and offshore vehicle preferences.
Sanctions Signal Distribution: Sanctions screening results, match confidence scores, PEP statuses, and high-risk jurisdiction flags distributed with realistic frequencies by niche. Middle East profiles carry higher PEP rates (~29%) and distinct jurisdictional exposure. LatAm profiles show higher risk ratings (~84% high). European and Swiss-Singapore profiles reflect the mixed legitimate-complex pattern that generates the most false positives.
Deterministic Reproducibility: Every KYC field is derived from a SHA-256 hash of the profile’s UUID. Same UUID, same sanctions signals, every time. This means you can run regression tests, change your screening thresholds, and compare results against a stable dataset — something impossible with randomly generated test data.
Pricing
| Tier | Records | Price | Best For |
|---|---|---|---|
| Compliance Starter | 1,000 | $999 | Threshold calibration, proof of concept |
| Compliance Pro | 10,000 | $4,999 | Full screening regression suite |
| Compliance Enterprise | 100,000 | $24,999 | AI model training + production screening validation |
No SDK. No API key. No sales call. Download a file, open it in Python or your screening platform, and run it through your sanctions engine. Count the alerts. Measure the false positive rate. Compare it to what your current test data produces.
Why This Matters Now
Enforcement is accelerating — and payment processors are primary targets. FinCEN, the FCA, and EU national regulators have made cross-border payment compliance a stated enforcement priority. The $586M Western Union settlement, the $120M Block penalty, and PayPal’s repeated enforcement actions are not outliers — they are the new baseline. Regulators are specifically examining whether screening systems were tested against realistic threat profiles, not just whether the technology existed.
The EU AI Act changes the equation. Fully applicable from August 2026, the EU AI Act classifies financial AI as high-risk under Annex III. Article 10 requires documented governance of training data — including provenance, bias assessment, and GDPR compliance. If your sanctions screening AI trains on real or anonymized client data, you need to prove compliance on both GDPR and AI Act simultaneously. Born-synthetic data eliminates both obligations: there is no PII to govern, no lineage to document, no re-identification risk to assess.
False positive rates are a measurable compliance risk. A screening system with a 95% false positive rate is not a screening system — it is a noise generator. When your compliance team processes thousands of false alerts per day, real sanctions matches get buried in the queue. Regulators have cited excessive false positive rates as evidence of inadequate screening — not just missed true positives. Testing against structurally complex profiles lets you calibrate thresholds that actually distinguish suspicious from complex.
The balance sheet test is open source. Every Sovereign Forger record passes algebraic validation: Assets – Liabilities = Net Worth. Run the Balance Sheet Test on our data, then run it on your current test data. If your test profiles do not pass basic financial coherence checks, your sanctions screening is calibrated against financially impossible profiles.
Every dataset ships with a Certificate of Sovereign Origin — documenting the born-synthetic methodology, zero PII lineage, and regulatory alignment. When your auditor or regulator asks “where did you get this screening test data?”, you hand them the certificate. When they ask “does this data contain any real person’s information?”, the answer is no — by construction, not by policy.
Stress-Test Your Sanctions Screening
Download 100 free KYC-Enhanced UHNWI profiles with sanctions screening signals, PEP indicators, and multi-jurisdictional exposure. Run them through your screening engine. Measure the false positive rate. Count how many edge cases surface that your current test data never generated.
That gap between what your test data covers and what your screening system encounters in production — that is where the next fine comes from.
No credit card. No sales call. Just your work email.
Related reading: PCI DSS Test Data — Why 4.0 Bans Real Cards in Test Environments — how PCI DSS 4.0 Requirement 6.5.4 prohibits production data in testing.
Frequently Asked Questions
How can payment processors test sanctions screening systems without exposing real cardholder data?
PCI DSS 4.0 Requirement 6.5.4, mandatory since March 2025, explicitly prohibits the use of live card data in test environments. Payment processors using Sovereign Forger’s born-synthetic profiles can populate sanctions screening pipelines with realistic transaction counterparties, including name variants, jurisdictional identifiers, and risk flags, across OFAC, EU, and UN lists, without ever touching real cardholder records. This eliminates PCI DSS breach risk while enabling high-fidelity QA coverage across all screening rule sets.
What edge cases in sanctions screening can born-synthetic financial data cover that generic test data cannot?
Generic test data rarely includes the nuanced edge cases that cause sanctions screening failures in production: transliterated name variants, partial OFAC matches, dual-nationality profiles, shell company ownership chains, and PEP-adjacent relationships across multiple jurisdictions. Sovereign Forger generates profiles purpose-built for Payment Services Regulation and cross-border AML requirements, including profiles with deliberate near-matches, clear negatives, and true positives across SDN, EU Consolidated, and UK HMT lists, giving QA teams structured coverage across all decision categories.
How does using synthetic sanctions data help payment processors demonstrate compliance with EU AI Act obligations during model audits?
EU AI Act Article 10 requires that datasets used to train or validate high-risk AI systems, including automated sanctions screening models, be representative, free of errors, and complete. Regulators auditing a payment processor’s screening model can demand documentation of training and test data provenance. Synthetic profiles from Sovereign Forger carry full generation metadata, zero lineage to real persons, and documented statistical distributions, giving compliance teams an auditable data trail that satisfies both EU AI Act Art.10 and GDPR Art.25 data-protection-by-design requirements simultaneously.
What does born-synthetic mean, and why does it matter specifically for sanctions screening in payment processing?
Born-synthetic means the data was generated entirely from mathematical distributions, specifically Pareto and related statistical models, with no source records derived from or linked to real individuals. Unlike anonymised or masked data, born-synthetic profiles have zero lineage to real persons, eliminating re-identification risk entirely. For payment processor sanctions screening, this distinction is critical: GDPR Art.25 requires privacy by design, and any test dataset with residual lineage to real data carries regulatory exposure. Born-synthetic data is compliant by construction, not by policy, making it defensible under regulatory examination without additional legal review.
How quickly can a payment processor’s compliance team get started with synthetic sanctions screening profiles?
Sovereign Forger provides 100 free KYC profiles available for instant download via a work email address, with no credit card required. Each profile contains 29 interlocked fields covering risk ratings, PEP status, sanctions screening flags, source of wealth narratives, and jurisdictional identifiers, all internally consistent and ready for direct ingestion into screening pipelines. The free tier is sufficient for initial integration testing, regression suite construction, and proof-of-concept demonstrations ahead of a full procurement decision.
Learn more about payment processor sanctions screening data and how Born Synthetic data addresses this in our glossary and comparison guides.